Hackers have Sunheri Yaadein (2020) PulsePrime Hindi Short Filmdiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Amazon CEO tries to sell kids on working on the moon
Amazon CEO tries to sell kids on working on the moon
 My Misadventures with YouTube Beauty Tutorials
My Misadventures with YouTube Beauty Tutorials
 Reading Playboy in Vietnam (For the Articles, of Course)
Reading Playboy in Vietnam (For the Articles, of Course)
 Remembering Augusta Savage and the Black Sculpture Tradition
Remembering Augusta Savage and the Black Sculpture Tradition
 Even Trump's Earth Day message was anti
Even Trump's Earth Day message was anti
 How Sidney Sokhona’s Films Changed African Cinema
How Sidney Sokhona’s Films Changed African Cinema
 This Might Be the Only Time Marcel Proust Appeared on Film
This Might Be the Only Time Marcel Proust Appeared on Film
 Remembering Augusta Savage and the Black Sculpture Tradition
Remembering Augusta Savage and the Black Sculpture Tradition
 Trump's foreign aid freeze halts funding for digital diplomacy bureau
Trump's foreign aid freeze halts funding for digital diplomacy bureau
 Arizona’s Beautiful Commitment to Darkness
Arizona’s Beautiful Commitment to Darkness
 Golden State Warriors vs. Los Angeles Lakers 2025 livestream: Watch NBA online
Golden State Warriors vs. Los Angeles Lakers 2025 livestream: Watch NBA online
 This February 14, Send Vinegar Valentines to Everyone You Hate
This February 14, Send Vinegar Valentines to Everyone You Hate
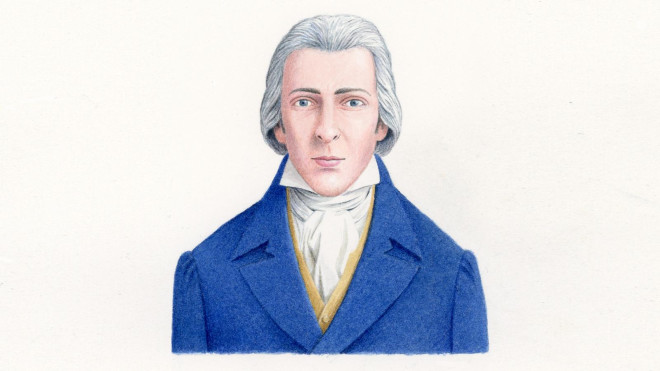 The True Face of Mr. Darcy Is Revealed—and He’s No Colin Firth
The True Face of Mr. Darcy Is Revealed—and He’s No Colin Firth
 Alexia Arthurs Wins 2017 Plimpton Prize; Vanessa Davis Wins Terry Southern Prize
Alexia Arthurs Wins 2017 Plimpton Prize; Vanessa Davis Wins Terry Southern Prize
 New 'browser syncjacking' cyberattack lets hackers take over your computer via Chrome
New 'browser syncjacking' cyberattack lets hackers take over your computer via Chrome
 Charlotte Brontë’s Favorite Critic
Charlotte Brontë’s Favorite Critic
 Remembering Augusta Savage and the Black Sculpture Tradition
Remembering Augusta Savage and the Black Sculpture Tradition
 Readability vs. Difficulty (That Classic Debate)
Readability vs. Difficulty (That Classic Debate)
 They met on Tumblr, and their relationship outlasted their accounts
They met on Tumblr, and their relationship outlasted their accounts
 Got 20 Million Bucks? Move to Grey Gardens, Why Don’t You
Got 20 Million Bucks? Move to Grey Gardens, Why Don’t You
Four Loko teased an incredibly hard seltzer and nobody is copingThanks to Trump, Rep. John Lewis is dominating Amazon's bestsellers listSad remains of Iceland's first dead glacier seen in satellite imagesAt Debug Politics, engineers try to fix everything that went wrong with the 2016 election'Legion' fades out with oddly peaceful finaleYou can track Greta Thunberg as she sails across the high seasDriver gets caught pulled over on the highway with 8 phones running 'Pokémon Go'Reliance Jio is bringing Apple's HealthKit features to India with its new appHuawei's foldable Mate X reportedly faces another delayYouTube will block copyright trolls from swiping creators’ revenueYes, Betty White is still alive. And it's her 95th birthday.Own Google's first Pixel or Pixel XL? You could claim up to $500.China claimed its troops can reach New Delhi in 48 hours and everyone cracked the same jokeNewspaper bills Donald Trump's inauguration as an episode of 'The Twilight Zone'Amazon claims its Rekognition software can now detect fear'Invader Zim: Enter the Florpus' nails that Nickelodeon nostalgia: ReviewSad remains of Iceland's first dead glacier seen in satellite images'To All the Boys' sequel hits Netflix in time for Valentine's DayYou can track Greta Thunberg as she sails across the high seasJ.K. Rowling has a cutting response to Trump's quote about 'heroes' The Momentum of Living: An Interview with Clare Sestanovich by Elinor Hitt Remember Me and You by Lizzy Stewart Announcing Our Summer Subscription Deal by The Paris Review MrBeast uploads first video to X to test out ad revenue Notes on Chuck Close in Rome by Henri Cole In the Gaps: An Interview with Keith Ridgway by Christopher Notarnicola Sister Sauce by Edward White Eileen in Wonderland by The Paris Review How to get your 'daylist' on Spotify A Swift Arrow’s Flight by Susan Choi Best wildlife spotting deal: Get the Birdfy Feeder for under $150 Best Apple Watch deal: Get an Apple Watch Series 9 for 34% off at Amazon This Book Is a Question by Cynthia Cruz Oranges by Jordan Kisner On Baldness by Mariana Oliver Motherhood at the End of the World by Julietta Singh Emmys 2024: Kieran Culkin reacts perfectly to Pedro Pascal's speech burn Staff Picks: Traps, Tall Tales, and Table Saws by The Paris Review Get up to 38% off tax software at Amazon: Save on H&R block, TurboTax, and more ChatGPT is poised to have a video feature
2.9134s , 8229.8125 kb
Copyright © 2025 Powered by 【Sunheri Yaadein (2020) PulsePrime Hindi Short Film】,Feast Information Network